Facial recognition data is the key to your identity, protect it well
Published: 28/04/2026
| The Conversation
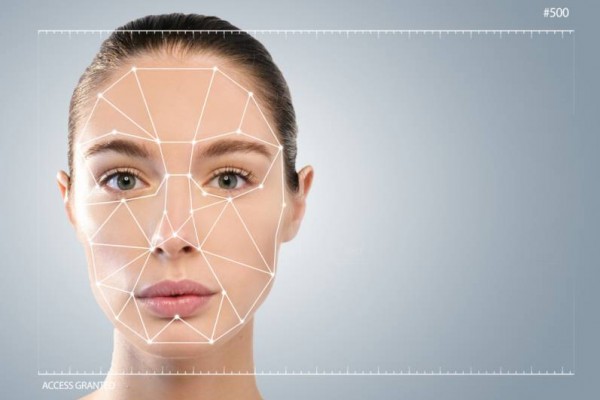
In an op-ed for The Conversation, Jonathan S. Weissman, Principal Lecturer of Cybersecurity at the Rochester Institute of Technology, discusses the growing prevalence of facial recognition technology (FRT) in society. The technology utilises cameras to scan faces and create mathematical templates of physical features. Weissman argues that, unlike passwords or credit cards, these biometric identifiers are permanent and cannot be reset if compromised. While templates are more secure than raw images, their theft creates lifelong vulnerabilities, potentially allowing unauthorised access to bank accounts and secure public infrastructure, such as airports.
The article also highlights the distinction between local and centralised storage. Many modern smartphones store biometric data on dedicated local hardware chips, preventing exposure during corporate or cloud breaches. In contrast, public surveillance systems often utilise centralised databases managed by third-party vendors, which may lack robust cybersecurity expertise. Weissman warns that if these systems are breached, a person’s facial template can act as a primary key, allowing criminals to link various stolen datasets and build extensive profiles of an individual's movements and personal records.
To mitigate these threats, Weissman calls for a privacy-by-design approach. Organisations are urged to encrypt all templates, minimise data retention, and employ advanced liveness detection to ensure systems interact with real people rather than digital forgeries. Transparency regarding data usage and restricted access remains essential for protecting long-term privacy.
Training Announcement: The IAPP Certified Information Privacy Technologist (CIPT) is a privacy-focused professional IT certificate from the IAPP that addresses data protection requirements and controls within complex technological environments. It explores the data lifecycle, privacy risk models and frameworks, the principles of Privacy by Design, and the role of privacy-enhancing technologies within the organisation. Find out more.
What is this page?
You are reading a summary article on the Privacy Newsfeed, a free resource for DPOs and other professionals with privacy or data protection responsibilities helping them stay informed of industry news all in one place. The information here is a brief snippet relating to a single piece of original content or several articles about a common topic or thread. The main contributor is listed in the top left-hand corner, just beneath the article title.
The Privacy Newsfeed monitors over 300 global publications, of which more than 3,250 summary articles have been posted to the online archive dating back to the beginning of 2020. A weekly roundup is available by email every Friday.

